Technical details
Wehe helps you identify when your ISP is slowing down certain apps – for example, giving slower speeds to YouTube and faster speeds to Netflix. Below we provide an overview of how the system works.
What is differentiation?
Differentiation is the practice of giving different Internet service to different applications. For example, an ISP may give worse performance to YouTube (leading to rebuffering and lower quality video), but allow Netflix to stream video at full resolution without rebuffering events. This is generally considered a violation of network neutrality.

Wehe is an app for Android and iOS that lets you test whether your ISP is giving you different performance for different apps. Specifically, we focus on traffic throttling --- where ISPs slow download speeds for an application.
ISPs typically implement differentiation by looking into the data transferred to your device, and applying throttling based on what they see. For example, to throttle YouTube traffic, the ISP will look for Internet traffic that looks like YouTube video streaming. When there is a match, the ISP will slow down that traffic based on a specific policy (e.g., lower transfer speeds to 1 Mbps).
How do we detect it?
To trigger differentiation, we need a way to send network traffic that looks like an application that might be throttled. Our approach is to record network traffic that an application generates, then replay that same traffic through Wehe. We recorded traces from popular applications such as YouTube, Netflix, Amazon Prime Video, Spotify, Skype and NBC Sports. In future releases, we will also allow you to record your own traffic to test.
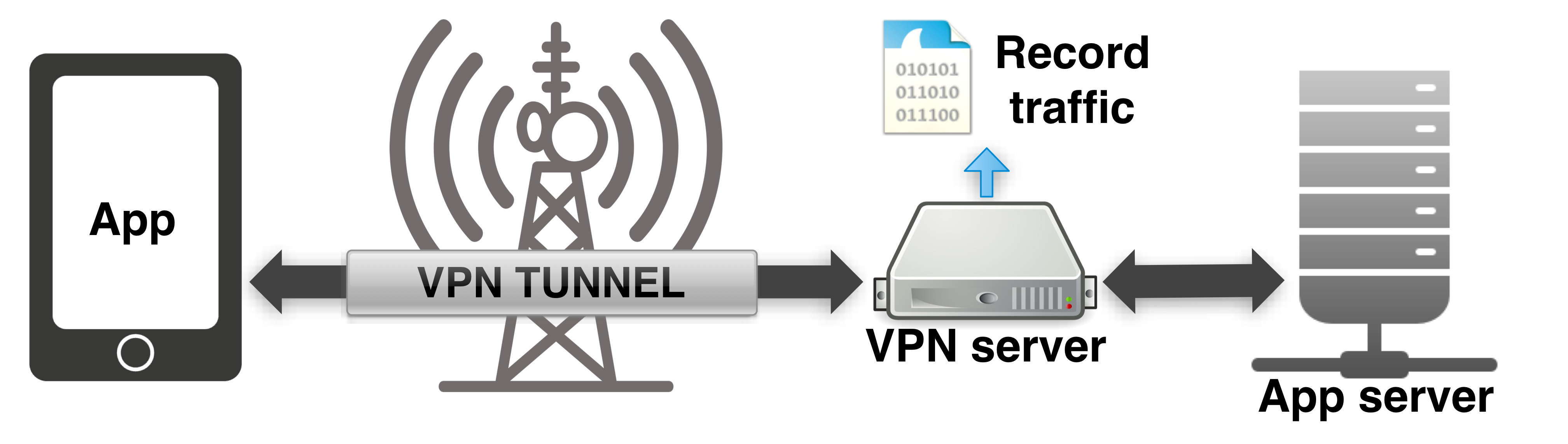
We then send that recorded traffic (we call this “replaying”) using the Wehe app, which should cause the traffic to be throttled if your ISP has a policy to slow down the replayed application. We confirmed that our tests will cause throttling to occur for several networks and commercially deployed traffic-throttling devices.
Once we trigger differentiation for a given application’s network traffic, we need to compare with network traffic that is not affected so we can confirm and quantify how much slower that traffic is. In other words, we need to send essentially the same traffic but make sure that your ISP does not apply throttling to it. How do we do it?
Recall that throttling is implemented by looking at the contents of your network traffic to see if it belongs to a given application. We can exploit this observation to “turn off” throttling as follows: we simply send the same traffic, but replace the original contents with random strings.
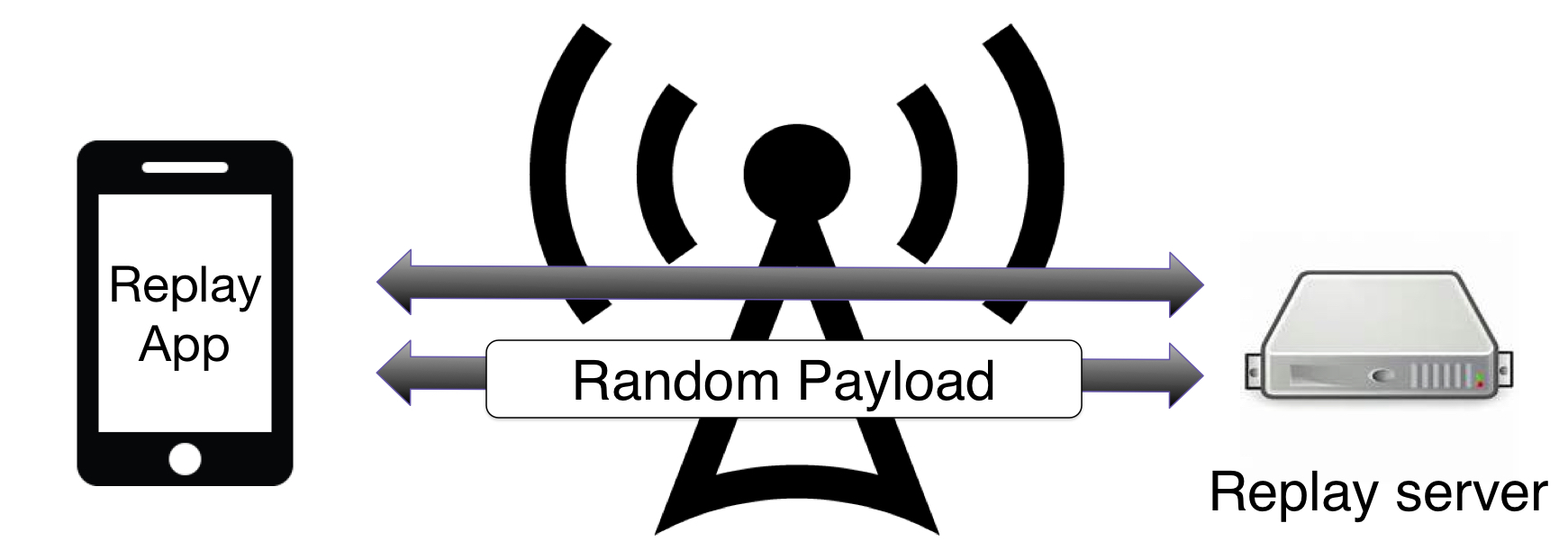
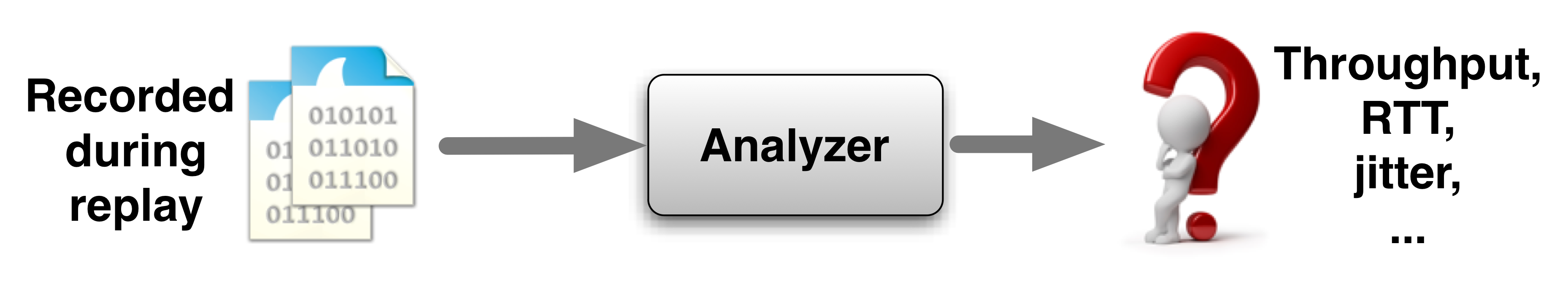
In summary, we replay traffic that we recorded from an app to expose it to potential throttling from your ISP. To determine whether that traffic was slower due to throttling (and not due to weak signal strength or an overloaded network), we send that same traffic with random strings as payloads, which cannot be throttled based on network traffic contents. If there is a difference, our app detects this and shows you the result.
How can I participate?
We identified 30 ISPs around the world that throttle traffic to lower speeds based on the application being used. We need your help to test more providers, in the US and worldwide, so we can understand how these policies change over time, location, and network. We are maintaining the Web page that publicize these practices, both to inform regulators and to allow consumers to make informed choices about selecting their mobile providers.
To test your network, install and run our free app for iOS, Android, and F-Droid.
More details
For more details about the Wehe methodology and the results from analyzing more than 1 million tests from more than 100,000 users, please check out our SIGCOMM 2019 paper.
Fangfan Li, Arian Niaki, David Choffnes, Phillipa Gill, Alan Mislove. A Large-Scale Analysis of Deployed Traffic Differentiation Practices. In Proc. of SIGCOMM, August 2019. (Link to paper)
Arash Molavi Kakhki, Abbas Razaghpanah, Hyungjoon Koo, Anke Li, Rajeshkumar Golani, David Choffnes, Phillipa Gill, and Alan Mislove. Identifying Traffic Differentiation in Mobile Networks.
In Proceedings of the 15th ACM Internet Measurement Conference (IMC'15), Tokyo, Japan, October 2015.
(Paper PDF | Poster | Presentation slides)